![]()
An awesome strip on how far too many essays are produced in University. Very truthful. Very painful.
![]()
An awesome strip on how far too many essays are produced in University. Very truthful. Very painful.
From a piece in The New York Times, we learn that
Rapid7 discovered that hundreds of thousands of businesses were investing in top-quality videoconferencing units, but were setting them up on the cheap. At last count, companies spent an estimated $693 million on group videoconferencing from July to September of last year, according to Wainhouse Research.
The most popular units, sold by Polycom and Cisco, can cost as much as $25,000 and feature encryption, high-definition video capture, and audio that can pick up the sound of a door opening 300 feet away. But administrators are setting them up outside the firewall and are configuring them with a false sense of security that hackers can use against them.
Whether real hackers are exploiting this vulnerability is unknown; no company has announced that it has been hacked. (Nor would one, and most would never know in any case.) But with videoconference systems so ubiquitous, they make for an easy target.
…
Two months ago, Mr. Moore wrote a computer program that scanned the Internet for videoconference systems that were outside the firewall and configured to automatically answer calls. In less than two hours, he had scanned 3 percent of the Internet.
In that sliver, he discovered 5,000 wide-open conference rooms at law firms, pharmaceutical companies, oil refineries, universities and medical centers. He stumbled into a lawyer-inmate meeting room at a prison, an operating room at a university medical center, and a venture capital pitch meeting where a company’s financials were being projected on a screen. Among the vendors that popped up in Mr. Moore’s scan were Polycom, Cisco, LifeSize, Sony and others. Of those, Polycom — which leads the videoconferencing market in units sold — was the only manufacturer that ships its equipment — from its low-end ViewStation models to its high-end HDX products — with the auto-answer feature enabled by default.
It sounds like there’s a whole lot of networking/IT admins who either should be fired (for doing a piss poor job of establishing network security) or resourced (if the reasons for the piss poor job is the result of understaffing and lack of proper training). Likely both are required.
Declan McCullagh has an article on an important case in the US, where a federal judge has demanded a defendant decrypt a PGP-encrypted drive for the authorities. Case law in the area of decryption is unsettled, as McCullagh notes:
The question of whether a criminal defendant can be legally compelled to cough up his encryption passphrase remains an unsettled one, with law review articles for at least the last 15 years arguing the merits of either approach. (A U.S. Justice Department attorney wrote an article in 1996, for instance, titled “Compelled Production of Plaintext and Keys.”)
Much of the discussion has been about what analogy comes closest. Prosecutors tend to view PGP passphrases as akin to someone possessing a key to a safe filled with incriminating documents. That person can, in general, be legally compelled to hand over the key. Other examples include the U.S. Supreme Court saying that defendants can be forced to provide fingerprints, blood samples, or voice recordings.
On the other hand are civil libertarians citing other Supreme Court cases that conclude Americans can’t be forced to give “compelled testimonial communications” and extending the legal shield of the Fifth Amendment to encryption passphrases. Courts already have ruled that that such protection extends to the contents of a defendant’s minds, the argument goes, so why shouldn’t a passphrase be shielded as well?
Eventually the case law around encryption has to be addressed by SCOTUS. There are too many differing positions at the moment; clarity is needed both for users of encryption in the US, and for counsel seeking to prosecute and defence clients.
Cory Doctorow being brilliant in sprucing up the metaphor that personally identifiable data is like nuclear waste. While the metaphor isn’t new, Doctorow does a great job as only a novelist can.
Every gram – sorry, byte – of personal information these feckless data-packrats collect on us should be as carefully accounted for as our weapons-grade radioisotopes, because once the seals have cracked, there is no going back. Once the local sandwich shop’s CCTV has been violated, once the HMRC has dumped another 25 million records, once London Underground has hiccoughup up a month’s worth of travelcard data, there will be no containing it.
And what’s worse is that we, as a society, are asked to shoulder the cost of the long-term care of business and government’s personal data stockpiles. When a database melts down, we absorb the crime, the personal misery, the chaos and terror.
I’ll let Mr. Vida explain, in his own words, why you should go and read his open letter:
Why listen to yet another open letter?
I helped build PlayBook. My team designed the PlayBook OS. We spent the better part of a year sequestered in secrecy working on what we believe to be a tablet OS experience at least as good as an iPad and, in many ways, better. We are immensely proud of our work there. We view the PlayBook OS as our baby. We want to see it succeed. We know the potential it has.
Seriously: go read the letter. It’s more personal, and richer in experience, than any of the analyst accounts of Heins, RIM, or the PlayBook. It’s also short, succinct, and well written. Read it.
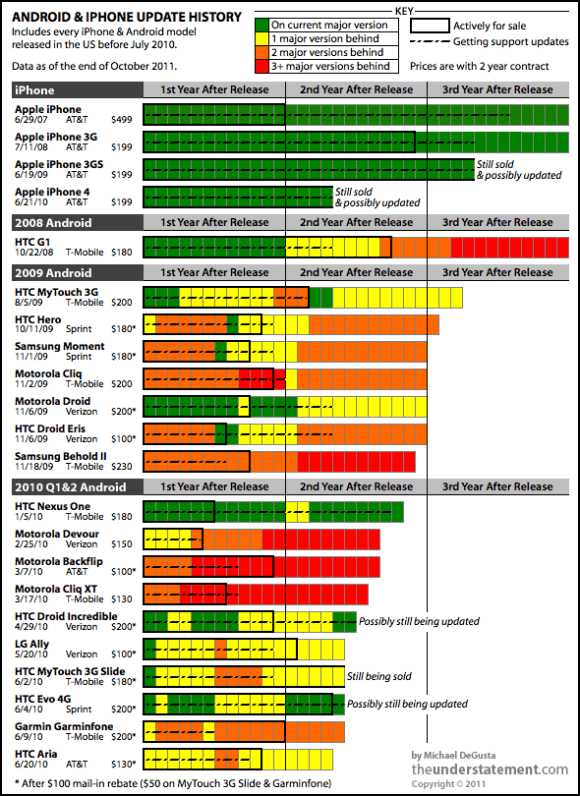
The seriousness of Android’s (lack of) security updates cannot be overstated. Phones that do not receive security updates can be subject to many of the most serious security attacks – such as man in the middle attacks, certificate-based MITM attacks, browser-based attacks, and so forth – and users remain ‘locked’ to their phones because of years-long contracts.
In essence, Android users on lengthy contracts with carriers are forcibly, contractually, linked to long-term security sinkholes.
This is an absolutely inexcusable situation, and one that Google, phone vendors, or carriers should be legislatively mandated to remedy.
…[Graham Thompson, president of Ottawa-based Intrinsec Security Technologies] cautions that RIM’s plans to tap into the Android marketplace could place a serious security burdern on the beleaguered company. An Android adherent himself, he nevertheless says the potential for breaches with Android apps threatens the core of RIM’s business strategy.
“I don’t understand why an [Android] application, for example, like a flashlight, requires Wi-Fi access or Internet access. It just makes no sense to me. Yet people are willing to say, ‘Yeah, go ahead. I don’t care about the privileges that this application is looking for. I just want my flashlight.’ And what impact does that have on corporate data is one of the main questions.”
I’m not exactly happy with the (impoverished) state of Android or iOS security. I’m happier (though I refrain from the full on “happy”) with RIM’s approach to data sharing with their app market (I’ve documented here some of the highly technical, and unwieldily, means that RIM notifies customers of security concerns). That said, I would wait before pronouncing that RIM’s integration of Android will lead to doom.
Specifically, those who have dealt with the RIM/Android integration have reported that Android apps do not get free reign on the device. This means that key Android ‘hooks’ are not always available, thus limiting the ‘damage’ they can do to a particular security profile.
Moreover, we cannot look at the integration without also considering the role of BlackBerry fusion, a system that intentionally hives off professional and personal ‘sections’ of the device. This segregation (in theory) should mean that even if an Android app breeches the RIM personal security protections, that the app should not have access to the professional side of the device and data contained in this element of the device.
Does this necessarily save the end-consumer, buying the device from Rogers, O2, or other wireless firm? No. Does it save businesses (a key market, and most zealous for, security assurance)? Much more likely.
Robert Sosinski has a good walkthrough of setting up GPG in OS X. Hopefully we’ll see some non-console-based instructions sometime in the near future to help those who are gun-shy when presented with a command prompt!
A really terrific paper on social media and ‘stranger danger’. You should read it.
I haven’t seen this argument before. It’s clever: stripping DRM (and/or transforming files to be cross-compatible with a variety of software readers) means that (in theory) those files will be accessible for longer periods of time, thus letting us preserve our (digital) history. From the article:
Piracy’s preserving effect, while little known, is actually nothing new. Through the centuries, the tablets, scrolls, and books that people copied most often and distributed most widely survived to the present. Libraries everywhere would be devoid of Homer, Beowulf, and even The Bible without unauthorized duplication.
The main difference between then and now is that software decays in a matter of years rather than a matter of centuries, turning preservation through duplication into an illegal act. And that’s a serious problem: thousands of pieces of culturally important digital works are vanishing into thin air as we speak.
At issue: I’m really not sure that a total archive of everything digital is actually something that we want, or necessarily need. A LOT of books, games, poems, and so forth were lost to the mists of time, and it’s not entirely clear to me that our world has fallen apart because of such losses.
History is a patchwork that is contingent on us perceiving certain items as more or less important from a partial and retrospective position. Moreover, it should be noted that truly significant texts/poems/artifacts have historically been replicated and distributed because of their value/importance at the time. Do we necessarily need a campaign of mass piracy – under the auspice of ‘preserving history’ – to ensure that similar efforts are made to secure the most critical elements of our past? I’m not so sure.