In the wake of the Toronto attack any number of journalists are trying to become experts on the ‘incel’ community, which defines itself as a community of men who are involuntarily celibate and as deserving intercourse with women. It’s led to some suggestions that maybe it’s appropriate to think about policy solutions to the ‘problem’. At issue, of course, is that some persons have failed to recognize the problem itself. Consider Ross Douthat, who links Amia Srinivasan’s ruminations on the links between desire and politics with incels, effectively conjoining a misogynistic subculture with “the overweight and disabled, minority groups treated as unattractive by the majority, trans women unable to find partners and other victims … of a society that still makes us prisoners of patriarchal and also racist-sexist-homophobic rules of sexual desire.” Douthat continues to ultimately argue that a combination of commerce, technology, and efforts to destigmatize sex work will lead to “at a certain point, without anyone formally debating the idea of a right to sex, right-thinking people will simply come to agree that some such right exists, and that it makes sense to look to some combination of changed laws, new technologies and evolved mores to fulfill it.”
Douthat’s entire argumentative structure — that the ‘problem’ to solve in an inability to engage in sexual, if not romantic, relationships — is predicated on the notion that there is such a thing as a legitimate right to intercourse. There is not. There is a legitimate right to safe, respectful, and destigmatized sexual relationships and activities. There is a right to sexual education, to sexual health and wellbeing, but there is no right to intercourse: such a right would imply that the act of penetrating another person is necessary and appropriate. That is clearly not the case.
Instead, the problem with the incel community is linked with misogyny. Specifically, as Jessica Valenti writes, the problem is with misogynist terrorism, a situation where certain men’s disdain towards women drives mass murders. Part of solving this particular problem is linked with addressing the underlying culture in America, and the world more generally. Specifically, she writes:
Part of the problem is that American culture still largely sees men’s sexism as something innate rather than deviant. And in a world where sexism is deemed natural, the misogynist tendencies of mass shooters become afterthoughts rather than predictable and stark warnings.
The truth is that in addition to not protecting women, we are failing boys: failing to raise them to believe they can be men without inflicting pain on others, failing to teach them that they are not entitled to women’s sexual attention and failing to allow them an outlet for understandable human fear and foibles that will not label them “weak” or unworthy.
It’s essential that men, and boys, learn about how to engage with other humans in non-destructive ways. Such a process is borderline revolutionary because it entails reshaping how cultural, social, legal, and economic relationships are structured, and any such restructuring must be motivated by a rebalancing of power relationships across genders and races (and, ultimately, geographies). The outcome will be that the privilege that straight white men have enjoyed for centuries will be diminished and, correspondingly, restrict the social and economic opportunities that some men have enjoyed solely because of their gender and race. But those changes are essential if we’re to actually confront the misogyny and racism that underlies not just incel culture, but that of mainstream society and politics as well.
Inspiring Quotation of the Week
Writing—I can really only speak to writing here—always, always only starts out as shit: an infant of monstrous aspect; bawling, ugly, terrible, and it stays terrible for a long, long time (sometimes forever). Unlike cooking, for example, where largely edible, if raw, ingredients are assembled, cut, heated, and otherwise manipulated into something both digestible and palatable, writing is closer to having to reverse-engineer a meal out of rotten food.
- David Rokoff
New Apps
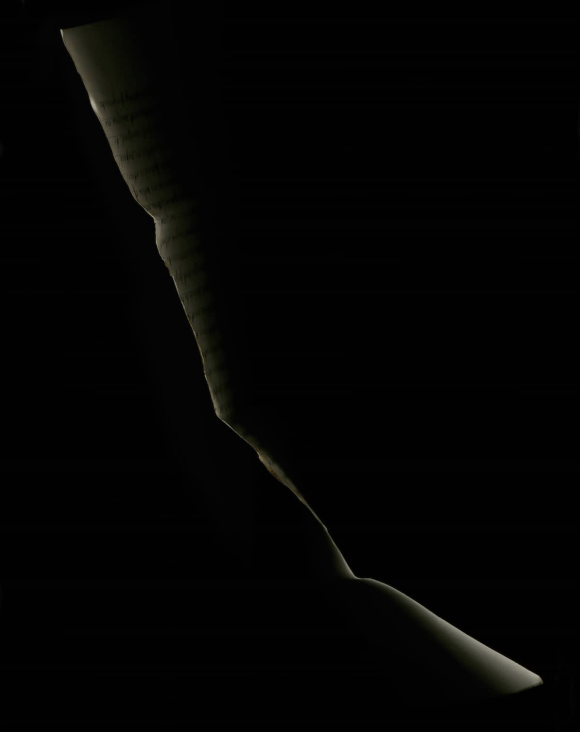
Great Photography Shots
I’d never seen x-ray photos of flowers before. It’s an absolutely breathtaking form of image making.


Music I’m Digging
Neat Podcast Episodes
Good Reads for the Week
- Janelle Monáe Frees Herself
- I tried leaving Facebook. I couldn’t
- Cape Town Residents Tell Us What It’s Like Living in the Shadow of ‘Day Zero’
- A Dying Scientist’s Rogue Vaccine Trial
- Pollution from Canadian refineries an ‘embarrassment’ compared to U.S.
- Millennials are struggling. Is it the fault of the baby boomers?
- When Misogynists Become Terrorists