![]()
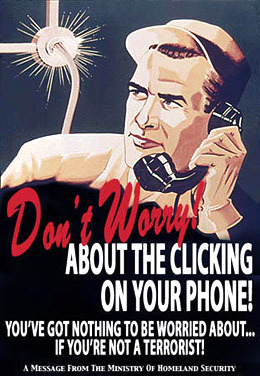
I’ll be watching you – from jaidurevertropfort
![]()
I’ll be watching you – from jaidurevertropfort
National mail carriers are important for loads of reasons, including legal protections around letters carried by them versus those carried by couriers. These mail carriers are far less agile than their private competitors and have been incredibly slow to recognize the need to change existing processes and practices. They desperately need to find new growth avenues to remedy declining gross and net revenues.
As a demonstration of how little Canada Post ‘gets’ the market and business it’s in today, we can turn to this comment:
Canada Post chief executive officer Deepak Chopra foresees a future in which consumers receive and pay their bills, get their paycheques, renew drivers’ licences, pay parking tickets, buy magazines and receive personalized ad pitches – all online, through ePost.
This isn’t a future: it’s the present. The only ‘future’ part of what he is outlining is that all these (already daily) functions would be routed through ePost. Unless Canada Post has an incredible value proposition – security, government mandates, or somehow implementing these functions better than existing services are mechanisms that immediately come to mine – I can’t see how the organization will exist in any semblance of what it is today, tomorrow.
[Computer specialists] are at once the most unmanageable and the most poorly managed specialism in our society. Actors and artists pale by comparison. Only pure mathematicians are as cantankerous, and it’s a calamity that so many of them get recruited by simplistic personnel men…[Managers should] refuse to embark on grandiose or unworthy schemes, and refuse to let their recalcitrant charges waste skill, time and money on the fashionable idiocies of our [computer] racket.
Herbert Grosch. (1966). “Programmers: The Industry’s Cosa Nostra,” Datamation 12(10): 202.
I admit it: I’m really curious to see how NFC technologies are adopted by various vendors and developers. To date, however, the integration has been poor and what adoption there has been tends to focus on payment solutions. Payment solutions scare the crap out of me because they increase the reasons attackers have to compromise my phone: it’s bad enough they want my personal information; I don’t want them after my digital wallet as well!
RIM has a neat bit of technology they’ve recently released, which leverages the NFC functionality in their new phones with Bluetooth pairing systems. Specifically, it enables rapid syncing between phones and audio-output devices (i.e., speakers). While the product is pretty “meh” as released today, it could be pretty exciting were vehicle manufacturers and speaker manufacturers to generally integrate NFC-pairing capabilities with their respective products. It’s presently a pain to listen to music stored on a mobile through vehicle speakers (using Bluetooth) or a friend’s speakers in their home. RIM has offered a partial solution to the Bluetooth pairing problem; now it’s up to the larger ecosystems to actually integrate RIM’s idea in a omnipresent and highly functional way.
Ars Technica has reported that a German court has found a victim of a phishing attack liable for successfully being phished. The finding is, at least in part, based on the bank’s position that they had previously warned customers about phishing attacks.
The court’s placement of liability is significant for a variety of reasons. Of course it’s important that the individual was victimized. The liability placement also defers expenses (likely through insurance) that the bank would have to assume were they at least partially liable for the customers’ actions. This said, we can understand (and perhaps disagree…) that, from a liberal position, individual citizens are responsible for their actions.
What is most significant are the consequences of placing liability on the individual. Specifically, it reduces the incentive that banks have to exercise their influence to address phishing. I’m not suggesting that the banks could hope to eliminate phishing by waving a gold-plated wand, but they are financially in a position to influence change and act on a global scale. Individuals – save for the ultra-rich – lack this degree of influence and power. While banks will be motivated to protect customers – and, more importantly, their customers’ money – if banks were found even partially liable for successful phishing attacks they would be significantly more motivated to remedy these attacks.
![]()
The secret room in most libraries
![]()
Small AT&T by Dan Moutal
Research conducted by Christopher Soghoian demonstrated that Dropbox lacks a security model that genuinely protects user data. As a consequence, while Dropbox is a convenient service it isn’t one that can really be trusted. Regardless, individuals around the world do, and will, continue to use the service.
Recognizing the user-constrains around cloud file-storage solutions, BoxCryptor has provided the tools to encrypt files before they are sent to Dropbox. This lets users rely on Dropbox for convenient storage while also reducing their risk profiles. All in all, it’s a win-win for the consumer.
The instructions are for OS X, Leopard, Snow Leopard, and Lion, and are relatively easy to follow. If you want to secure yourself a little bit better than you likely are right now you’d be well served to set up automatic encryption now. As an added bonus, the instructions will let you also choose Microsoft’s or Google’s cloud services so long as you point the “EncFS Raw Path” to the file path of these other services (don’t worry: it’ll be super clear what that refers to as you go through the instructions!).
While it’s certainly not definitive, and it doesn’t walk you through using each and every tool, Edwards has a good high-level overview piece that is worth reading.